In the first part of this three-part series, I went over what happens when your security posture is broken. In my job at Acronis, I regularly analyze ransomware, and its destructive behavior. Using the example of LockBit 2.0 ransomware, our computer may have been able to keep running, but once the attack got in, the ransomware didn’t stop encrypting documents and other sensitive files until it was done. Even restarting the computer wasn’t enough to stop the attack. Here’s the thing with relying on being insignificant enough to not be an obvious target: it doesn’t matter. You are still a target if you are vulnerable, and the chances of coming out of the situation without any data loss are minuscule. Of course, you can do things with a partial protection solution, even though you may not be able to stop the attack or save all of your files. These options include tools that range from built-in or free tools to paid solutions that will at least minimize the impact of an attack on your computers.
Stop in the name of the Task Manager
The great thing about Task Manager is that it is a part of Windows by default. MacOS and most Linux distributions also have their own versions of this, and they all work similarly. For this example, let’s just assume that you happen to notice something going on with your system. Maybe it’s running slower, the fans kick in when they normally wouldn’t, or you even happen to catch the file extensions beginning to change. Great, you have an opportunity to stop the ransomware before you have lost everything. It’s easy, just right-click on the taskbar, and open the Task Manager. If you click on the More details link at the bottom of the window, you can see the Lockbit22.exe – or whatever the name is that the file is given by the attacker – in the Task Manager window, so it’s a quick right-click, and you can stop the ransomware before it does any more damage.

There are a couple of problems with this scenario. One is that you need to be familiar enough with Windows to recognize any processes that are unusual, and the other is that it relies on the ransomware allowing the task manager to stop it, and not having already set up automation to restart the ransomware after it has been stopped. If this works, you may have just saved yourself the massive headache of having all of your important files encrypted. Maybe it doesn’t work, and you need something a little more powerful.
Exploring your options
A fairly common tool that is used by researchers is Process Explorer, which is part of the SysInternals Suite provided by Microsoft. This is not installed by default but is easy to find on Microsoft’s website. Process Explorer is like Task Manager on steroids, but it works very similarly. Again, you can right-click on the process, and stop it with either Kill Process or Kill Process Tree. Again, you have to be familiar with what you should expect to see running in order to identify something that is out of place. While it is more likely that the process will be stopped with this application, we still have to hope that the ransomware won’t automatically start up again.

Starting over
If you remember from my last article, I rebooted the computer, and the ransomware started up again after I stopped the process. I had used Process Explorer, but this only stopped the malware until the computer was restarted. The ransomware had updated registry settings and ensured that it would automatically start up again when Windows booted up. Of course, the ransomware isn’t listed in the Startup Apps – that would be too easy. We need to get into the registry and clean up what the ransomware has done there. Everything else has been fairly easy up until this point, so before a reboot, I should be able to clean up these changes, right?
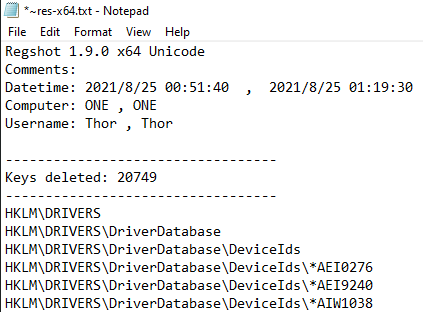
There is a tool called RegShot that lets you take two snapshots of the Windows registry, and compare them. I took a snapshot before running LockBit, and again after the ransomware finished running. This is where your heart sinks as you start seeing the number of changes to the registry. Over 20,000 keys were deleted.
Almost another 82,000 keys were added in that same timeframe.

You might be able to narrow it down some, maybe by searching for keywords like “lockbit” in the log. This isn’t an efficient way to ensure you have cleaned all traces of the changes made by the ransomware, because it is very likely that the ransomware did not use its own name in every change. Perhaps you try, and perhaps you get the computer back to normal operation, without risking the ransomware being started up again. At this point, the ransomware still exists on the system. From the Task Manager or Process Explorer, we have the file name, we can search in Explorer for this file, and will most likely be able to delete it. This ignores a common trick employed by ransomware, which is to drop additional files, which have a different name but are additional copies of the ransomware, or additional malware payloads.
Since we’re now likely in the land of make-believe, let’s pretend that you deleted all of the copies of the ransomware and any other malware from your computer. You have also restored the registry to its former glory – a task that is only recommended for experienced professionals. By stopping the ransomware, you may have even saved some of your files. The thing is, you still have encrypted files. There are two options here, pay the ransom in the hopes that the attackers are nice enough to give you the decryption key, or maybe you’re lucky enough to have all of the affected files in a cloud storage service like Google Drive or Microsoft OneDrive. Most people don’t back up all of their files to these services, and most of the time don’t have enough storage available to do so.
The end is near
This is where I get overly honest. Everything I just outlined is an oversimplification of this scenario. I didn’t even mention possible changes to Group Policy or other tactics used by ransomware groups. The fact is, if you are caught unprotected, it is unlikely you will be able to fully recover. Ransomware gangs are getting more sophisticated, and often just scan the internet for vulnerable computers to attack without regard to who the target is. The only way to ensure you won’t become a victim is to be prepared ahead of time. This means a multi-layered solution to protect your computer from future attacks.
We’ve seen what happens when your computer is attacked, and now we’ve seen how enough diligence, and probably research, can help us to largely get back to normal after the attack. In the third and final part of this series, we’ll dive into what it takes to make sure you don’t become a victim of LockBit in the first place.

Topher Tebow is a cybersecurity researcher, focusing on community collaboration and threat analysis. Topher has been working with malware and other cyberthreats for more than a decade, beginning with web-based malware before moving into endpoint protection. Topher has written technical content for several companies, covering topics from security trends and best practices, to the analysis of malware and vulnerabilities. In addition to being published in industry publications like Cyber Defense Magazine and Security Boulevard, Topher has contributed to articles by several leading publications, and spoken at international cybersecurity events.

We had a client done by LockBit 2.0 ransomware and it was devastating. Using group policy to deploy it to every computer on the network and everything was encrypted. It highlighted a bigger security risk to the client that I warned them about not months earlier. You can bet they signed up to the extra security now.
Things I’ve seen combat this is Datto RMM Ransomware Detection and SentinelOne. These are the only packages I’ve seen realtime stop the exe’s from doing too much damage across the network. It’s only part of the solutions to help protect our clients as a MSP.